Configure Server-Wide SAML
Configure server-wide SAML when you want all single sign-on (SSO) users on Tableau Server to authenticate through a single SAML identity provider (IdP), or as the first step to configuring site-specific SAML in a multi-site environment.
If you have configured server-wide SAML and are ready to configure a site, see Configure Site-Specific SAML.
The SAML configuration steps we provide make the following assumptions:
You are familiar with the options for configuring SAML authentication on Tableau Server, as described in the SAML topic.
You have verified that your environment meets the SAML Requirements, and obtained the SAML certificate files described in those requirements.
Before you begin
As part of your disaster recovery plan, we recommend keeping a backup of certificate and IdP files in a safe location off of the Tableau Server. The SAML asset files that you upload to Tableau Server will be stored and distributed to other nodes by the Client File Service. However, these files are not stored in a recoverable format. See Tableau Server Client File Service.
Note: If you use the same certificate files for SSL, you could alternatively use the existing certificate location for configuring SAML, and add the IdP metadata file to that directory when you download it later in this procedure. For more information, see Using SSL certificate and key files for SAML in the SAML requirements.
If you are running Tableau Server in a cluster, then the SAML certificates, keys, and metadata file will be automatically distributed across the nodes when you enable SAML.
This procedure requires that you upload the SAML certificates to TSM so that they are properly stored and distributed in the server configuration. The SAML files must available to the browser on the local computer where you are running the TSM web interface in this procedure.
If you have gathered and saved the SAML files to the Tableau Server as recommended in the previous section, then run the TSM web interface from the Tableau Server computer where you copied the files.
If you are running the TSM web interface from a different computer, then you will need to copy all SAML files locally before proceeding. As you follow the procedure below, browse to the files on the local computer to upload them to TSM.
Open TSM in a browser:
https://<tsm-computer-name>:8850. For more information, see Sign in to Tableau Services Manager Web UI.
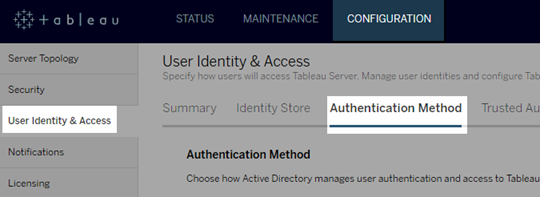
On the Configuration tab, select User Identity & Access, and then select the Authentication Method tab.
For Authentication Method, select SAML.
In the SAML section that appears, complete Step 1 in the GUI, entering the following settings (do not yet select the check box to enable SAML for the server):
Tableau Server return URL—The URL that Tableau Server users will access, such as https://tableau-server.
Using https://localhost or a URL with a trailing slash (for example, http://tableau_server/) is not supported.
SAML entity ID—The entity ID uniquely identifies your Tableau Server installation to the IdP.
You can enter your Tableau Server URL again here. If you plan to enable site-specific SAML later, this URL also serves as the base for each site’s unique ID.
SAML certificate and key files— Click Select File to upload each of these files.
If you are using a PKCS#8 passphrase-protected key file, you must enter the passphrase with TSM CLI:
tsm configuration set -k wgserver.saml.key.passphrase -v <passphrase>After you provide the information required in Step 1 in the GUI, the Download XML Metadata File button in Step 2 in the GUI becomes available.
Now select the Enable SAML authentication for the server check box above Step 1 in the GUI.
Complete the remaining SAML settings.
For Steps 2 and 3 in the GUI, exchange metadata between Tableau Server and the IdP. (Here’s where you might need to check in with the IdP’s documentation.)
Select Download XML Metadata File, and specify the file location.
If you are configuring SAML with AD FS, you can return to Step 3: Configure AD FS to accept sign-in requests from Tableau Server of “Configure SAML with AD FS on Tableau Server.”
For other IdPs, go to your IdP account to add Tableau Server to its applications (as a service provider), providing the Tableau metadata as appropriate.
Follow the instructions in the IdP’s website or documentation to download the IdP’s metadata. Save the .xml file to the same location that holds your SAML certificate and key files. For example:
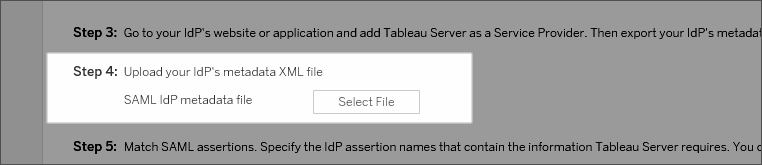
C:\Program Files\Tableau\Tableau Server\SAML\idp-metadata.xmlReturn to the TSM web UI. For Step 4 in the GUI, enter the path to the IdP metadata file, and then click Select File.
For Step 5 in the GUI: In some cases, you may need to change the assertion values in the Tableau Server configuration to match the assertion names that are passed by your IdP.
You can find assertion names in the IdP's SAML configuration. If different assertion names are passed from your IdP, then you must update Tableau Server to use the same assertion value.
Tip: “Assertions” are a key SAML component, and the concept of mapping assertions can be tricky at first. It might help to put this in a tabular-data context, in which the assertion (attribute) name is equivalent to a column heading in the table. You enter that “heading” name, rather than an example of a value that might appear in that column.
For Step 6 in the GUI, select the Tableau applications in which you want to give users a single sign-on experience.
Note: The option to disable mobile access is ignored by devices running Tableau Mobile app version 19.225.1731 and higher. To disable SAML for devices running these versions you must disable SAML as a client login option on Tableau Server.
For the SAML sign-out redirect, if your IdP supports single logout (SLO), enter the page you want to redirect users to after they sign out, relative to the path you entered for the Tableau Server return URL.
(Optional) For Step 7 in the GUI, do the following:
Add a comma-separated value for the
AuthNContextClassRefattribute. For more information about how this attribute is used, see SAML compatibility notes and requirements.Specify a domain attribute if not sending the domain as part of the username (i.e.,
domain\username). For more information, see When running multiple domains.
Click Save Pending Changes after you've entered your configuration information.
Click Pending Changes at the top of the page:

Click Apply Changes and Restart.
In your web browser, open a new page or tab, and enter the Tableau Server URL.
The browser redirects you to the IdP’s sign-in form.
Enter your single sign-on user name and password.
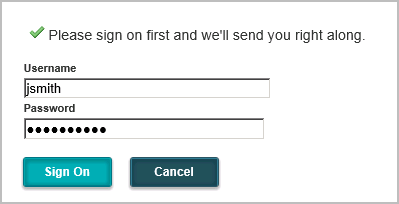
The IdP verifies your credentials and redirects you back to your Tableau Server start page.
